- What is CVE-2025-55315?
- Why this vulnerability stands out
- Attack mechanics: How HTTP Request Smuggling works
- Who is affected & versions to track
- How to mitigate the risk now
- Blue-Team checklist: detection, response, testing
- Why defenders should care
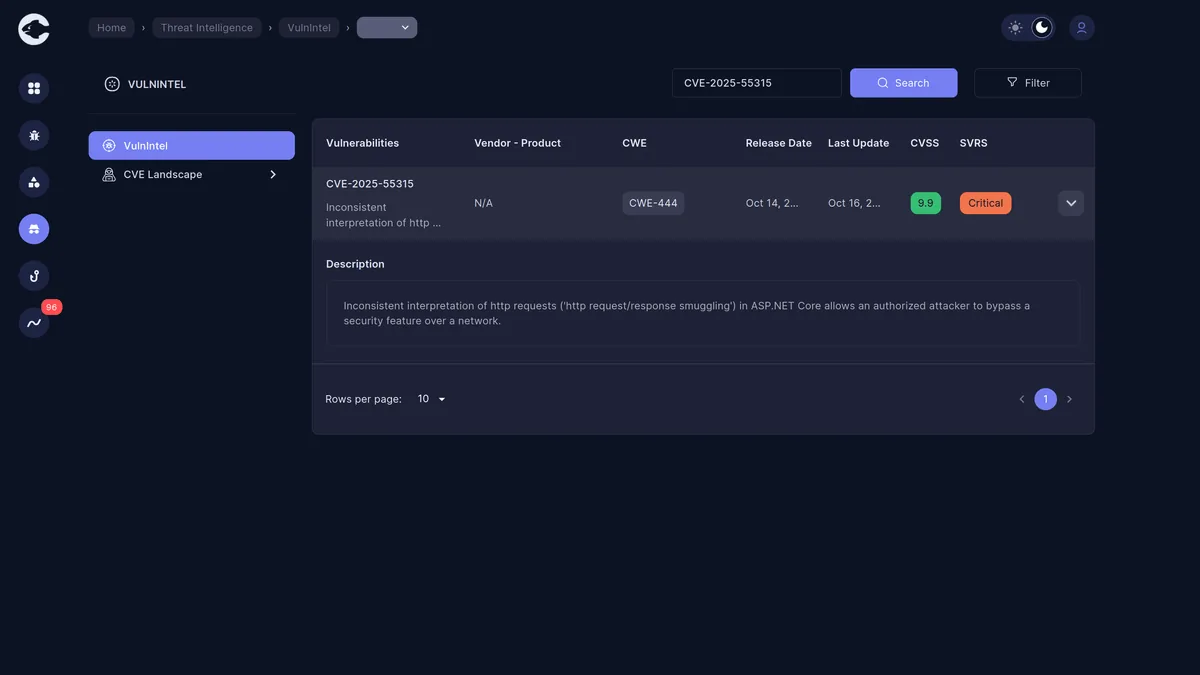
What is CVE-2025-55315?
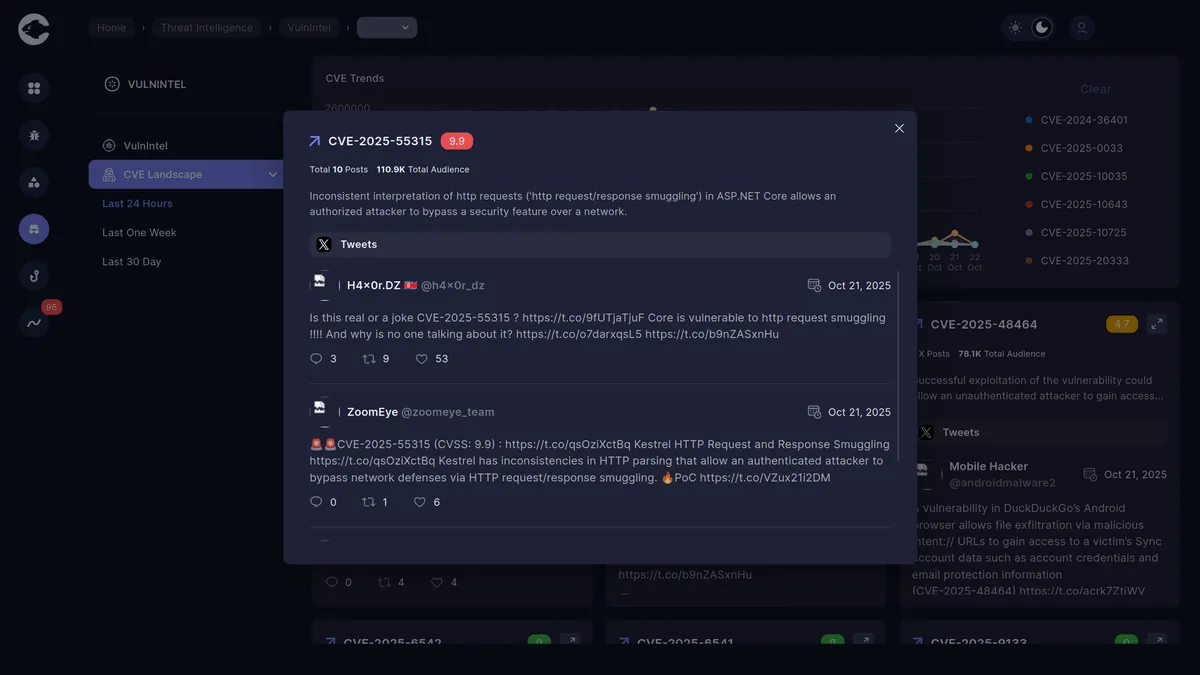
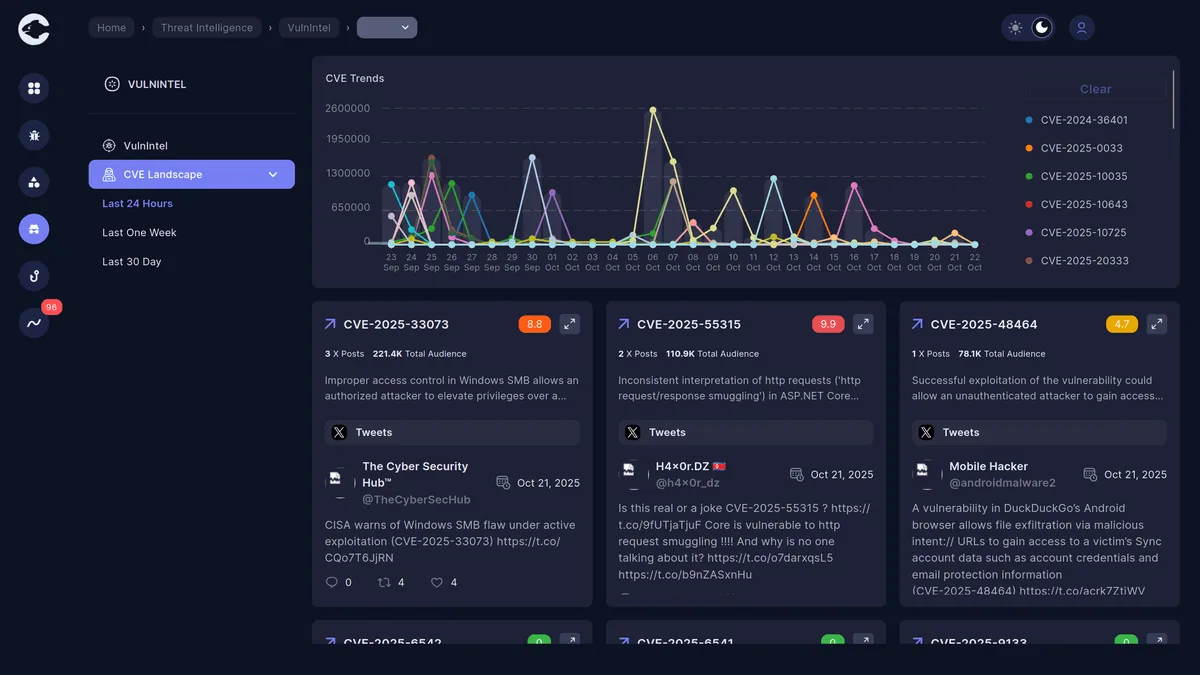
This vulnerability is an "inconsistent interpretation of HTTP requests" (an HTTP request/response smuggling variant) in ASP.NET Core (via its Kestrel web server component) that allows an attacker, under certain conditions, to bypass a security feature over a network. The reported base CVSS 3.1 score is 9.9 (Critical): AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:L. In plain terms: an attacker could sneak hidden or manipulated HTTP requests through the server, potentially hijack other users' sessions, access sensitive data, modify files, or force a crash.
Why this vulnerability stands out
- The sheer severity (9.9) is unusually high for request-smuggling flaws in this stack; specialist write-ups call it "the highest-ever severity in ASP.NET Core context".
- It exploits the HTTP layer (requests/responses) rather than typical logic flaws — meaning it's potentially impactful across many applications built on the framework.
- Because it's in a core web-server component (Kestrel), it affects a broad range of web apps rather than a niche plugin or module.
- The vulnerability can enable multiple threat outcomes: credential theft, bypass of protections (like CSRF, authorization controls), SSRF-style internal request chaining, or file tampering.
How the HTTP Request Smuggling works (attack mechanics)
-
The attacker crafts an HTTP request (or series of requests) that exploit differences in how intermediaries (proxies/load-balancers) and the server itself parse headers like Transfer-Encoding, Content-Length, or ambiguous boundary/terminator behavior. This enables a "smuggled" secondary request to be hidden within a legitimate one (or part thereof).
-
Because the server (ASP.NET Core Kestrel) mis-interprets the boundaries/terminators, the hidden request is processed in addition to or instead of the intended request.
-
The attacker may abuse this to:
- Perform actions as another user or escalate privileges
- Bypass authorization/CSRF/antiforgery controls
- Cause the server to make internal requests (SSRF) or act on behalf of the attacker
- Modify file content, exfiltrate data or cause service disruption/denial of service
-
The severity (confidentiality, integrity, availability) is high because all three can be impacted depending on the app's logic and deployment.
Who is affected & versions to track
- Products impacted: ASP.NET Core (various versions) and the Microsoft.AspNetCore.Server.Kestrel.Core package.
- Affected version ranges (via vendor/researcher summarisation):
- ASP.NET Core version 6.0.0 to 6.0.36 (inclusive)
- ASP.NET Core version 8.0.0 to 8.0.20 (inclusive)
- ASP.NET Core version 9.0.0 to 9.0.9 (inclusive)
- Microsoft.AspNetCore.Server.Kestrel.Core version 2.3.0 or earlier
- The vulnerability requires network-accessible HTTP endpoints served by Kestrel; thus web applications built on those frameworks and deployed unpatched are at risk.
- Because many enterprise apps may run older framework versions (6.x, 8.x) or may self-host Kestrel, the exposure is broad.
How to mitigate the risk now
- Immediate actions (within hours):
- Apply the vendor patches/updates for ASP.NET Core / Kestrel as soon as available.
- For applications still on affected versions, schedule update/upgrade to versions beyond the fixed versions.
- If immediate patching is not possible, mitigate exposure by restricting external access to Kestrel endpoints:
- Place web servers behind a hardened reverse-proxy that enforces strict parsing and header checks.
- Use a Web Application Firewall (WAF) that supports detection/prevention of HTTP request smuggling patterns (ambiguous headers, dual encodings, Transfer-Encoding + Content-Length mismatches).
- Review cloud-hosting or container orchestration configurations to ensure endpoints are not exposed to internet without proper filtering.
- Short-to-mid-term actions (days):
- Conduct an inventory of all ASP.NET Core applications and versions in your environment; tag those using Kestrel directly or self-hosted.
- Implement monitoring/logging for anomalous HTTP request patterns: suspicious header combinations (Transfer-Encoding + Content-Length), unexpected multiple requests within a single TCP connection, or unexpected internal requests generated by the app post-request.
- Harden application logic: ensure input validation, enforce authentication/authorization for all endpoints, validate internal request-routing logic for SSRF/forwarding paths.
- Long-term actions (weeks):
- Upgrade all applications to the latest supported LTS versions of .NET/ASP.NET Core and ensure self-hosted servers use latest Kestrel builds.
- Review application architecture: avoid exposing Kestrel directly to untrusted networks without a proxy; adopt zero-trust internal access models.
- Incorporate HTTP request smuggling awareness and testing into your secure development lifecycle (SDL). Perform code/review tests for ambiguous header handling, boundary parsing, and ensure proxies and application servers interpret HTTP consistently.
Blue-Team checklist (operational)
-
Inventory: List all web apps built on ASP.NET Core; note versions, hosting model (IIS, Kestrel self-hosted, containers).
-
Patch & verify: Confirm the update has been applied; test in staging that the app still correctly handles HTTP requests and that headers like Transfer-Encoding, Content-Length are processed safely.
-
Detection rules:
- Log when inbound requests include both Transfer-Encoding and Content-Length headers or other suspicious header combos.
- Monitor for unusually small or empty request bodies with large Content-Length values or chunked encodings that don't match body size.
- Watch for downstream internal requests initiated by the app soon after an external request (possible SSRF or request-smuggled chain).
-
Hunt/back-scan: Use logs to search for prior exploitation indicators: header-anomalies, large volumes of requests with ambiguous encoding, internal requests logged without corresponding external request.
-
Containment playbook: If you detect exploitation: isolate the affected server, collect logs + memory dump, disable external access to the app, rebuild from patched code, conduct root-cause analysis.
-
Test: In a safe lab environment, simulate HTTP request smuggling variations (ambiguous headers, dual encodings) against a test ASP.NET Core deployment to validate detection rules and patch efficacy.
Why defenders should care
This vulnerability represents a high-impact web-layer threat for many enterprise applications. Because it targets a core web framework component, its reach is broad. If exploited, the attacker could bypass security controls that many organizations rely on (authentication/authorization/CSRF), access or tamper with data, and even disrupt service availability. Given the 9.9 severity, this should be treated as a priority-one patch and exposure identification should be immediate. Failing to address it could place your web-applications in serious jeopardy of compromise.
Related reading from Cypho:
- OSINT and Internet Scanning Platforms Matter — discover exposed and vulnerable services before attackers do using practical OSINT tools
- Attack Surface Management — continuously monitor your infrastructure for unpatched vulnerabilities and misconfigurations



