Unknown Threats Are Unstoppable - Until We Expose Them
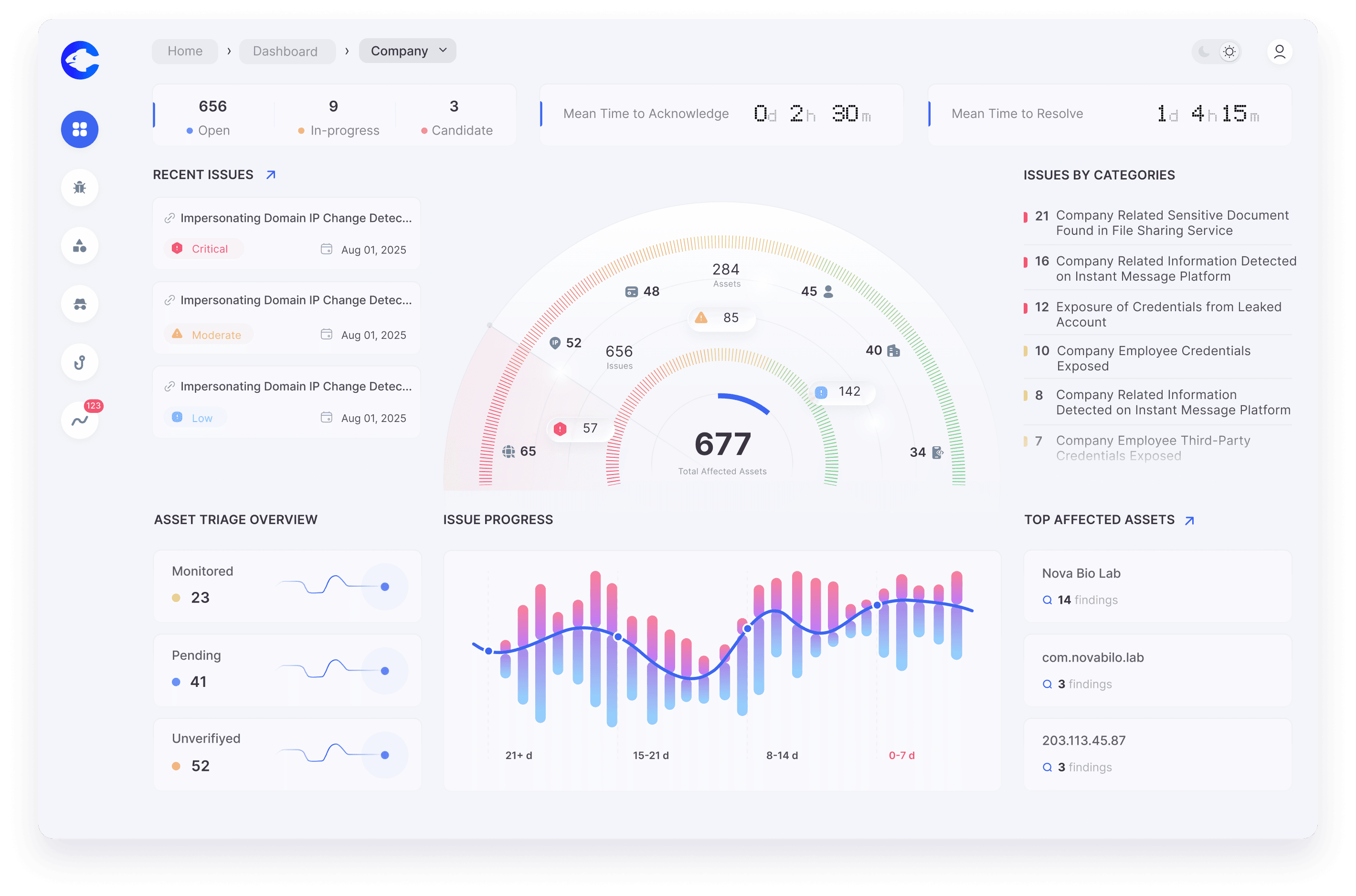
Cypho provides 360-degree visibility into your threat landscape through continuous monitoring of digital assets in deep, dark and clear web to analyze, prioritize, and remediate effectively.
How Cypho works
From Scanning to Remediation: Continuous Threat Exposure Management
Integrated Threat Intelligence to continuously monitor & mitigate cyber risks
Built for Security Experts, by Security Experts

Discover Latest Vulnerabilities
Cypho's raw intel pool allows you to stay one step ahead of attackers. Analyze information about techniques, methods to maintain a solid security posture.
Why CYPHO?
Cypho empowers the synergy of automation, AI, and human expertise to deliver end-to-end threat intelligence. We ensure continuous threat monitoring against emerging threats, safeguarding your organization from vulnerabilities.
Expert Analyst review
Ensuring accurate insights with expert review
AI-powered detection
Detecting threats with advanced AI algorithms tuned for cyber crime databases
24/7 customer support
Team of experts standing by to support you all the time
Faster issue creation
Delivering real-time notifications for critical risks
Customized pricing
Effective usage tailored to your specific needs
Self-serve interface
Delivering comprehensive threat intelligence in intuitive formats.
False-positive elimination
Empowering accuracy with state-of-art threat intelligence
Extensive data collection
Uncovering hidden threats through vast network of clear and dark web source
Industries that Choose Cypho
Cypho addresses the growing needs of various industries with continuous threat exposure management while ensuring the integrity of businesses.
Ecommerce
Protect online markets from fraud, phishing, data breaches, account takeovers through enhanced digital risk protection
Government
Research, investigate, and protect sensitive data from nation-wide threats and cyber crime organizations.
Telecom
Providing secure networks via checking open ports, misconfigurations, outdated certificates, improper access control.
Oil & Gas
Identify targeted threats and supply chain risks and defending energy operations
Finance
Shield financial systems from credential leak, fraud, compliance risks. ensuring integrated risk protection
Healthcare
Safeguarding medical data and systems from leaks, attacks, and impersonation threats.
Experience Next Generation Threat Intelligence
Minimize complexity and maintain secure posture with real-time monitoring and actionable insights




